bochert john (6 Ergebnisse)
Suchfilter
Produktart
- Alle Product Types
- Bücher (6)
- Magazine & Zeitschriften (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Comics (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Noten (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Kunst, Grafik & Poster (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Fotografien (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Karten (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Manuskripte & Papierantiquitäten (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
Zustand Mehr dazu
- Neu (5)
- Wie Neu, Sehr Gut oder Gut Bis Sehr Gut (1)
- Gut oder Befriedigend (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Ausreichend oder Schlecht (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Wie beschrieben (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
Einband
Weitere Eigenschaften
- Erstausgabe (1)
- Signiert (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Schutzumschlag (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- Angebotsfoto (5)
Sprache (1)
Preis
- Beliebiger Preis
- Weniger als EUR 20 (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
- EUR 20 bis EUR 40
- Mehr als EUR 40
Gratisversand
- Kostenloser Versand nach USA (Keine weiteren Ergebnisse entsprechen dieser Verfeinerung)
Land des Verkäufers
Verkäuferbewertung
-
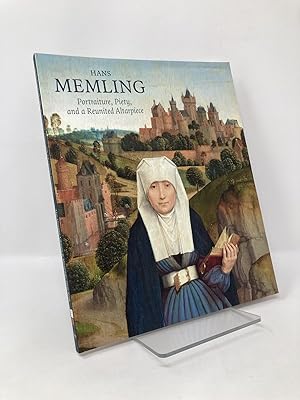
Hans Memling: Portraiture, Piety, and a Reunited Altarpiece
Sprache: Englisch
Verlag: Paul Holberton Publishing, 2020
ISBN 10: 1911300083 ISBN 13: 9781911300083
Anbieter: Southampton Books, Sag Harbor, NY, USA
Erstausgabe
Trade Paperback. Zustand: Like New. First Edition. First Edition, First Printing. Published by Paul Holberton Publishing, 2016. Quarto. Pictorial wraps. Book is like new; clean with no writing or names. Sharp corners and spine straight. Binding tight and pages crisp. Covers have very light shelf wear and sticker residue on back. 112 pages. ISBN: 9781911300083. 100% positive feedback. 30 day money back guarantee. NEXT DAY SHIPPING! Excellent customer service. Please email with any questions or if you would like a photo. All books packed carefully and ship with free delivery confirmation/tracking. All books come with free bookmarks. Ships from Southampton, New York. We Buy Books! Individual titles, libraries, collections. Message us if you have books to sell!
-
Software and Critical Technology Protection against Side-Channel Analysis through Dynamic Hardware Obfuscation
Anbieter: Ria Christie Collections, Uxbridge, Vereinigtes Königreich
EUR 54,29
EUR 13,85 Versand
Versand von Vereinigtes Königreich nach USAAnzahl: Mehr als 20 verfügbar
In den WarenkorbZustand: New. In.
-
Software and Critical Technology Protection Against Side-Channel Analysis Through Dynamic Hardware Obfuscation
Sprache: Englisch
Verlag: Creative Media Partners, LLC Mai 2025, 2025
ISBN 10: 1025122186 ISBN 13: 9781025122182
Anbieter: AHA-BUCH GmbH, Einbeck, Deutschland
Taschenbuch. Zustand: Neu. Neuware - Side Channel Analysis (SCA) is a method by which an adversary can gather information about a processor by examining the activity being done on a microchip though the environment surrounding the chip. Side Channel Analysis attacks use SCA to attack a microcontroller when it is processing cryptographic code, and can allow an attacker to gain secret information, like a crypto-algorithm's key. The purpose of this thesis is to test proposed dynamic hardware methods to increase the hardware security of a microprocessor such that the software code being run on the microprocessor can be made more secure without having to change the code. This thesis uses the Java Optimized Processor (JOP) to identify and _x SCA vulnerabilities to give a processor running RSA or AES code more protection against SCA attacks.
-
Software and Critical Technology Protection Against Side-Channel Analysis Through Dynamic Hardware Obfuscation
Sprache: Englisch
Verlag: Creative Media Partners, LLC Mai 2025, 2025
ISBN 10: 1025118685 ISBN 13: 9781025118680
Anbieter: AHA-BUCH GmbH, Einbeck, Deutschland
Buch. Zustand: Neu. Neuware - Side Channel Analysis (SCA) is a method by which an adversary can gather information about a processor by examining the activity being done on a microchip though the environment surrounding the chip. Side Channel Analysis attacks use SCA to attack a microcontroller when it is processing cryptographic code, and can allow an attacker to gain secret information, like a crypto-algorithm's key. The purpose of this thesis is to test proposed dynamic hardware methods to increase the hardware security of a microprocessor such that the software code being run on the microprocessor can be made more secure without having to change the code. This thesis uses the Java Optimized Processor (JOP) to identify and _x SCA vulnerabilities to give a processor running RSA or AES code more protection against SCA attacks.
-
Software and Critical Technology Protection against Side-Channel Analysis through Dynamic Hardware Obfuscation
Anbieter: moluna, Greven, Deutschland
EUR 61,74
EUR 48,99 Versand
Versand von Deutschland nach USAAnzahl: Mehr als 20 verfügbar
In den WarenkorbZustand: New. KlappentextrnrnSide Channel Analysis (SCA) is a method by which an adversary can gather information about a processor by examining the activity being done on a microchip though the environment surrounding the chip. Side Channel Analysis attacks .
-
Software and Critical Technology Protection against Side-Channel Analysis through Dynamic Hardware Obfuscation
Sprache: Englisch
Verlag: Creative Media Partners, LLC Nov 2012, 2012
ISBN 10: 1288307195 ISBN 13: 9781288307197
Anbieter: AHA-BUCH GmbH, Einbeck, Deutschland
Taschenbuch. Zustand: Neu. Neuware - Side Channel Analysis (SCA) is a method by which an adversary can gather information about a processor by examining the activity being done on a microchip though the environment surrounding the chip. Side Channel Analysis attacks use SCA to attack a microcontroller when it is processing cryptographic code, and can allow an attacker to gain secret information, like a crypto-algorithm's key. The purpose of this thesis is to test proposed dynamic hardware methods to increase the hardware security of a microprocessor such that the software code being run on the microprocessor can be made more secure without having to change the code. This thesis uses the Java Optimized Processor (JOP) to identify and _x SCA vulnerabilities to give a processor running RSA or AES code more protection against SCA attacks.